NRK recently published, that a message that was sent to the alleged kidnappers in 2018, asked to see a picture of Anne-Elisabeth Hagen face. The message itself, “cee face ae”, was written in the ‘data language’ hex. This means that it could be easily read directly from the bitcoin blockchain, without being decoded first. By revealing the message, NRK indirectly revealed which addresses were used in the cryptic communication exchange in the Hagen case. This means, in theory, that anyone can now pretend to be either Tom Hagen or the alleged kidnappers by sending messages to the address.
Bitcoin transactions are easily traceable
Bitcoin has an open blockchain, which means that all transactions can be tracked, and all data entered into the system can be read by everyone. This is one of the reasons many criminals avoid using bitcoin.
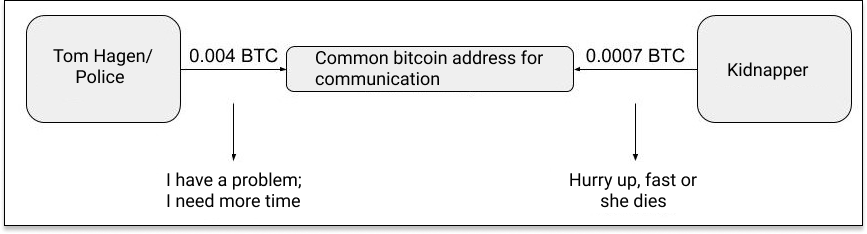
Bitcoin experts in Arcane Crypto, the parent company of the Kryptografen, quickly found the “cee face ae” message and the bitcoin address associated with it. They could then see the communication between the two parties. It is the same addresses used over time and the parties have communicated to a common address instead of directly to each other’s digital wallets.
It is as if they were using a common mailbox, where they can only add information and read what is already in the box. None of the content added can be deleted.
Several messages that broke with the layout of the threat letter
The experts in Arcane Crypto, where able to reveal the whole dialogue. Initially, the messages were to be exchanged by sending pre-agreed amounts, where the significance of the various amounts was written in the threat letter. Neither Kryptografen nor the experts in Arcane Crypto, have seen the full letter explaining the codes, but after searching open forums online, they quickly found someone who claims to have an overview of what the different amounts have meant.
Overview of transactions and dialogue on bitcoin:
Messages in parentheses are written by Tom Hagen/Norwegian police, and not part of the alleged kidnapper’s code table for messages. The messages were originally written in Norwegian.
Date Amounts Messages/Meaning
- 2020-05-29: 0.001 “I confirm that I want to pay”.
- 2019-01-16: 0.0007 “Hurry up, fast or she dies”.
- 2019-01-02: 0.0007 “Hurry up, fast or she dies”.
- 2019-01-02: 0.0007 “Hurry up, fast or she dies”.
- 2018-12-27: 0.000706 “Hurry up, fast or she dies”.
- 2018-12-14: 0.000706 (cee face ae)
- 2018-12-10: 0.0007001 “Hurry up, fast or she dies”.
- 2018-12-10: 0.0007001 “Hurry up, fast or she dies”.
- 2018-12-10: 0.000706 (decode hex in monero to asci)
- 2018-12-10: 0.000706 (dec0de)
- 2018-12-01: 0.0007 “Hurry up, fast or she dies”.
- 2018-12-01: 0.0007 “Hurry up, fast or she dies”.
- 2018-12-01: 0.0007 “Hurry up, fast or she dies”.
- 2018-11-30: 0.000706 “Hurry up, fast or she dies”.
- 2018-11-30: 0.000706 “Hurry up, fast or she dies”.
- 2018-11-13: 0.004 “I have a problem; I need more time”.
- 2018-11-10: 0.0007 “Hurry up, fast or she dies”.
- 2018-11-02: 0.03 “I am sending monero in seven days».
Appears amateurish
After going over all the transactions, several interesting factors stick out. First, the alleged kidnappers appear to be technical amateurs. A cryptocurrency expert in Arcane, Torkel Rogstad, points out the reasons why:
“The clearest sign, is the lack of expertise is the reuse of bitcoin addresses,” says Rogstad. “This is considered very harmful to the recipient’s privacy. The best practice is to generate new addresses every time you send and receive bitcoin, and something all bitcoin wallets allow you to do.”
Are there other things that stand out? “It looks as though the alleged kidnappers have recycled the money sent to the communication address. This is another data point that may reveal the kidnapper’s identity. If they had taken precaution, and not reused their addresses, and also left the communication address untouched, the blockchain analysis would have been considerably more difficult to carry out”.
Furthermore, it is interesting to see that the first message that probably came from the counterparty, on November 10, 2018, was sent from the crypto exchange Huobi. According to Rogstad, this could potentially reveal who the sender is, if the police obtain information from the exchange.
Hagen/the police tried to move the conversation to Monero
It is also worth noting that the “cee face ae” messages is not the first time Hagen/the police broke with the layout that was created in the threat letter. On December 10, 2018, they also sent an extra message asking them to actually move the dialogue over to Monero. The message Hagen/the police sent then was “decode hex in monero to ascii”, which probably means that they sent a message in Monero and that it must be decoded to ascii in order to become readable. We do not have the opportunity to know if the dialogue was actually transferred to Monero or not. Monero is an encrypted blockchain, so the information will not be openly available as on bitcoin.





